Contents list
Service Lineup to Meet Diverse Needs
PS Solutions offers a wide range of IT technology-based services, leveraging the wealth of expertise it has accumulated as a subsidiary of group companies of SoftBank Corp. We support a wide range of corporate issues with the power of technology.
Services for Small and Medium-sized Enterprises

Your Reliable Partner for Internal IT Operations
As a subsidiary of SoftBank Corp. we offer our group’s IT support expertise to as many customers as possible, and our IT professionals deliver comprehensive support for challenges in the information system business.
Services for Group
Companies of SoftBank Corp.
Promoting further growth of the Group
with the power of IT
PS Solutions provides a wide variety of IT solutions to subsidiaries of SoftBank Corp.
With the Group’s corporate philosophy of “Information Revolution — Happiness for everyone” in mind, we provide support for a variety of IT issues by leveraging our wealth of knowledge and expertise. We provide optimal services that address your specific concerns.
Our lineup of services ranges from IT operations support to security diagnosis, so please feel free to contact us for any IT-related concerns you may have.
- 01Oracle
Product Sales & Support - PS Solutions is an official partner of Oracle Corporation Japan. We sell software licenses for Oracle products and provide product support 24/7. We support smooth introduction and operation of Oracle products with our extensive support system.


- 02One StopIT Support Services
-
This service supports the corporate IT operations of subsidiaries of SoftBank Corp.We offer customized services with AI-generated chatbots that serve as OA support contact points for procurement, operation, purchasing, and disposal, complemented by “comprehensive support” from a team of IT specialists.
Our extensive experience in providing support to group companies enables you to utilize our services with confidence.
“IT Support Services” Overview
For basic queries (via AI-generated chatbots), our AI leverages insights from our comprehensive support history to offer quick answers 24/7. For more complex issues that exceed the chatbot’s capabilities, direct support from our experienced staff
is readily available.
- Procurement

-
- Procurement of equipment and software at corporate prices.
- It’s also possible to opt for a temporary PC subscription.
- Kitting
-
- Setting up initial kitting procedures
- It’s also possible to continuously update these procedures
- Handling PC kitting requests, providing quotes, and managing delivery
- Help Desk

-
- Generated AI provides immediate response to PC and software consultations
- Support staff manned for issues not resolved by AI consultation
- Operation Outsourcing
-
- Device management and system operation
- Management and operation of business software
- Purchase and Disposal
-
- Device collection and disposal
- Data erasure and purchase
Main Scope of “Comprehensive Support”
We provide support for both regularly occurring and temporary operations, according to the customer’s needs.
- Help Desk Operation
- Responding to inquiries from within the company, remote support (available when the environment is prepared at the customer’s end)
- Security Operation
- Support for work related to SoftBank Corp. security requests (PIGNUS)
- Documentation Operation
- Customer support (creation of procedure manuals, work on behalf of customers, etc.)
- PC Management Operation
- PC (Win/Mac) initialization, kitting, trouble-shooting, storage, disposal/purchase, entry/exit support, procurement, device inventory support
- Device Management Operation
- Microsoft Intune operations agency (device registration, deletion, application distribution, patch application), device control
- Account Management Operation
- Account registration, deletion, configuration changes, inventory support
(Microsoft Entra ID, Microsoft 365, zoom, BOX, Slack, SalesForce, Okta, GWS)
- IT Asset Management Operation
- IT asset ledger management (HW/SW) registration, deletion, modification, inventory support
(MaLionCloud, LanScope, BusinessConcier, Jamf)
Service Features

-
Procurement leveraging scale
We handle products from as many as 4,000 manufacturers, enabling us to procure according to our clients’ requirements. We can provide products at low prices by purchasing in bulk from our cooperating partners.

-
Extensive track record and know-how
We provide high quality services based on our extensive experience in supporting group companies. We utilize our experience and know-how organized and systematized data with pre-trained generation AI to speedily respond to customer inquiries.

-
Flexible adjustment of request time
Flexible adjustment of request time is possible according to the customer’s situation.
Three Reasons to Choose PS Solutions

-
1. Support experience for group companies
We have a wealth of experience in supporting group companies of SoftBank Corp., and can respond in accordance with SoftBank Corp. standards.

-
2. Cost reduction
We can outsource at low cost, which leads to cost savings compared to hiring new personnel at group companies.

-
3. Peace of mind that only a group company can provide
Because we are a member of the SoftBank Corp., you can use our services with peace of mind.
- 03Access Security ServicePSSOL Gateway
-
PSSOL Gateway is a SaaS service that both ensures secure communication channels and manages account and device verification. Use of cloud services and applications is on the rise with the spread of remote work. We provide secure, worry-freeremote access solutions that address advances in security requirements in our ever-changing world.
We cover the entire domestic market in East and West Regions, and are able to respond to business continuity plans (BCP) in the event of disasters or other emergencies.
Shifts in Security Models
With the rising popularity of cloud services and spread of remote work, security requirements are growing more sophisticated by the day. Security these days cannot be maintained with conventional perimeter defense models for internal and externalnetwork environments.
Zero Trust security is making headlines in light of this situation. Zero Trust is a new security model that views all access as “untrustworthy” whether it comes from within or outside the network, subjecting it to verification and preventingthreats to valuable information assets and systems.
Security using the Zero Trust model will become the standard in the near future!
Perimeter Defense Model
Resources kept safe
by securing network perimeter
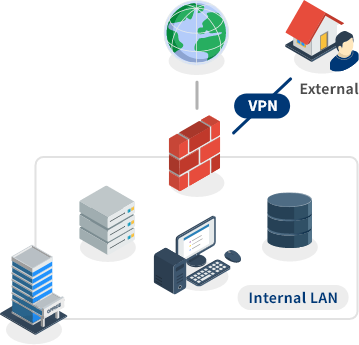
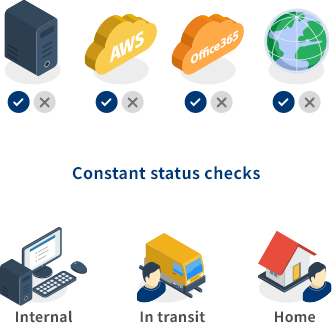
Zero Trust Model
Constant checks for trust depending on user/device status,
granting access privileges to resources
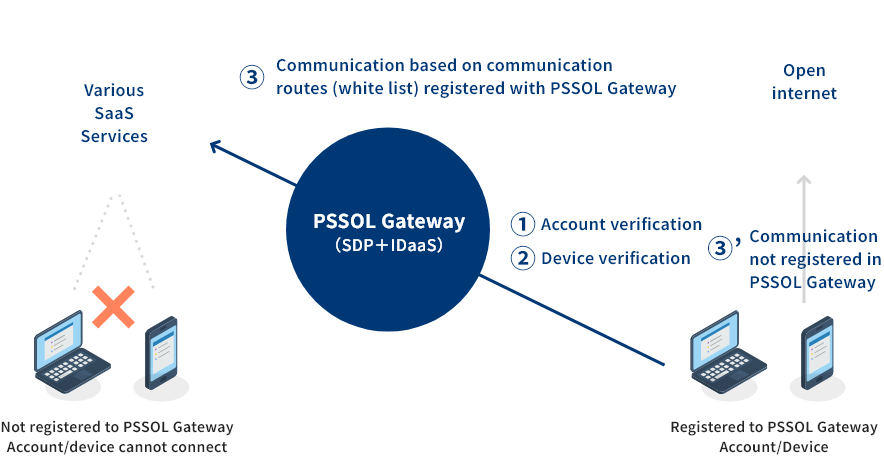
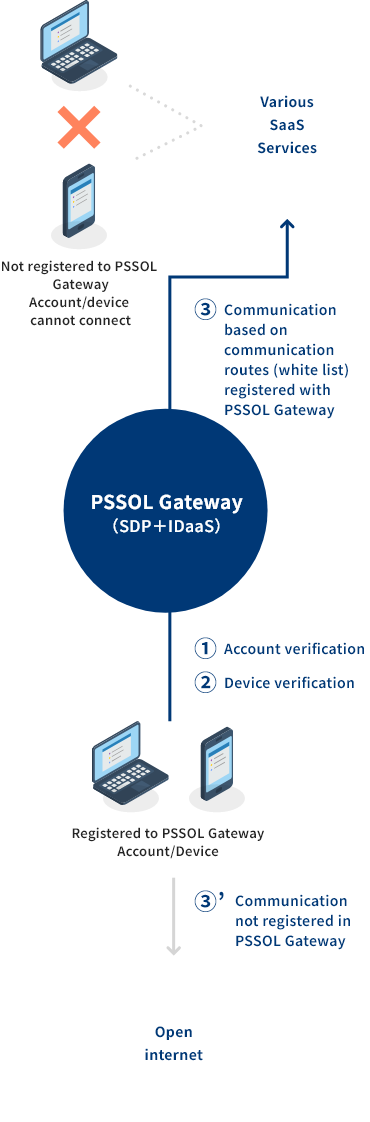
PSSOL Gateway Service Overview
PSSOL Gateway is a SaaS service consisting of a set of “Appgate SDP” – a Cloud Security Alliance Software Defined Perimeter-compliant secure access framework solution by Appgate Inc. – and “Azure AD” – a cloud-based ID and access control service provided by Microsoft.
-
(1) Ensures a secure communication channel
・PSSOL Gateway uses a security framework to secure communication channels.
PC Target OS Guaranteed OS version Windows 10 or later MacOS 11.7 to 13.x Mobile Applicable OS Guaranteed Version iOS/iPadOS 15.2 or later Android 11 or later As of February 1, 2024
-
(2) Account and device verification
・Account authentication is performed by SAML 2.0. SAML2.0
・If you do not have IDaaS, you can authenticate with an Appgate Local account using two-factor authentication (Authenticator).
・Each device verification is confirmed via AppgateSDP.※Certified Account Verification Infrastructure
Microsoft EntraID, Okta, GlugentGate, LOCKED -
For companies using SaaS service with fixed IP
Secure and reliable remote access is provided in about one month after signing a contract.Account management and connection
(IDaaS Connect)Enhanced security via device verification
Accessible from any device, inside or outside the office
No IT staff required
-
- ●appgate SDP
- Appgate Inc. provides a secure access framework solution that complies with the Cloud Security Alliance’s Software Defined Perimeter.
- ●IDaaS(ID as a Service)
- Account management service, a product that enables unified account integration by linking IDaaS with other products.
- ●SAML(Security Assertion Markup Language)
- A standard for communicating the identity of users to web applications and services
“Zero Trust Security”
Distrusts all communication, evaluates access privileges in all case
Service Type Details
| Gateway Sharing Type | ||
| Communication Image | 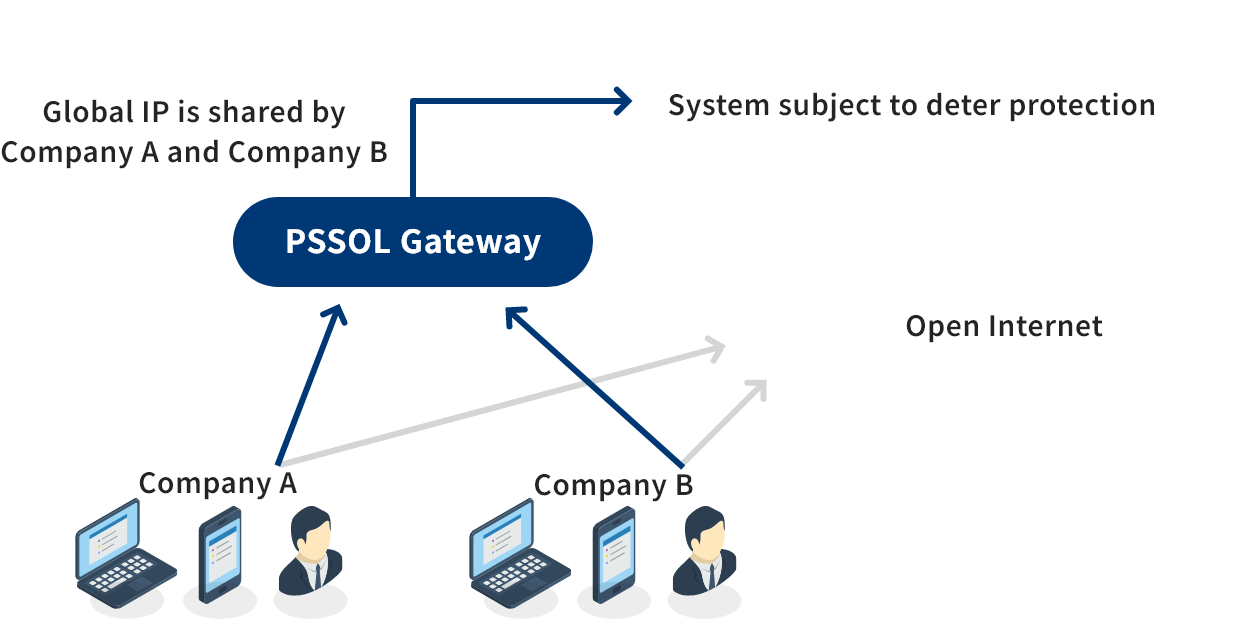  |
|
| Features | This type shares the Global IP assigned to the gateway among customers housed in the gateway. This type is recommended for customers who do not need to occupy the fixed IP (Global IP). | |
Service Hours, Inquiry Methods, etc.
| Service Hours | 24/7 Excluding maintenance downtime. |
|---|---|
| Inquiry response time (Business hours) |
Weekdays from 9:30 to 17:00 After hours/Saturdays, Sundays, and national holidays: Will be handled on the next business day. |
| Inquiry Method | |
| Maintenance | Notification 1 month prior to implementation |
| Troubleshooting |
|
Flow of Introduction

STEP 1
Consideration of introduction (Q&A and decision to adopt the system)

STEP 2
Contract signing

STEP 3
Confirmation of terminal information/communication route information

STEP 4
Gateway construction and Global IP system registration

STEP 5
Setup the installer and configuration file on the terminal

STEP 6
Start to use
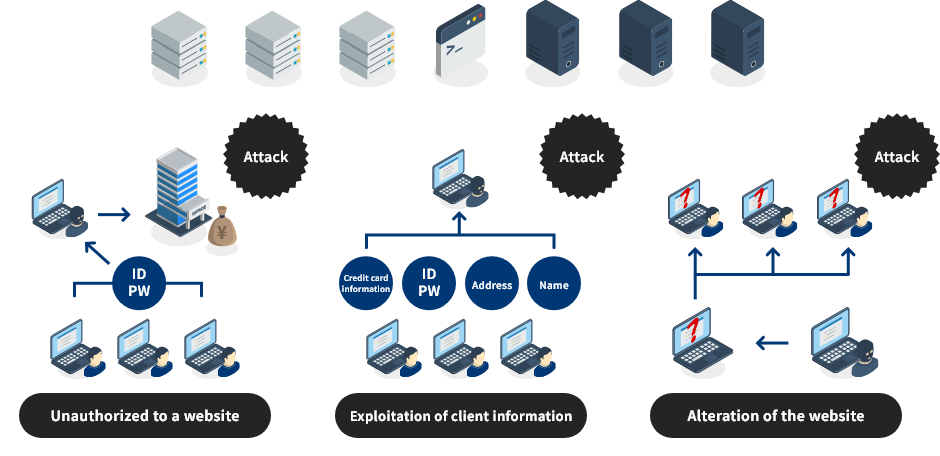
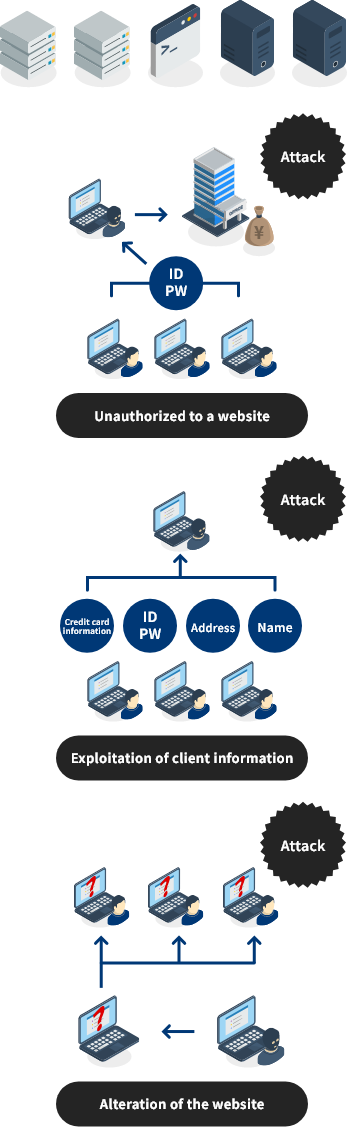
- 04Vulnerability Assessment Service
- This is a service to diagnose potential vulnerabilities of your website (OS, middleware, web applications, etc.) by attempting various simulated attacks from an attacker’s point of view. If vulnerabilities are found, we will provide you with knowledge to take countermeasures against cyber attacks. To protect your valuable websites, please take advantage of our “Vulnerability Assessment Service” to understand the security risks and how to respond to them.
Cyberattacks are on the rise!
Customer’s Website
3 Rules of Cybersecurity Management
- 01
- Top management must be aware of cybersecurity risks and take the lead in implementing countermeasures, while continuing to promote use of IT.
- 02
- Security measures must of course include in-house operations, but also affiliates, supply chain business partners, and IT system administration contractors.
- 03
- There must be proper communication with related parties, including disclosure of information related to cybersecurity risks, countermeasures, and responses, both on a regular basis and in event of an emergency.
Service
- Web Application Diagnosis
-
Main Assessment items
- Cross-site scripting
- SQL injection
- Command injection
- Directory traversal
- Authentication bypass
- Privilege elevation etc.
- Network Diagnosis
-
Main Assessment items
- Surveys of network services including DNS, FTP, file sharing, SSH, SNMP, database servers
- Surveys of web server vulnerabilities
- Known vulnerabilities in various OS and NW devices
- Checking service status and port status etc.
Use Case
- Information Service
- Corporate sites, service sites, HR systems, search systems, health check systems
- Logistics
- Online retail sites, corporate sites, electronic contract systems, e-commerce sites, sales management systems, sales campaign sites
- HR Services
- Corporate sites, corporate information sites for members, user management systems, recruitment sites
- Power
- Corporate sites, monitoring systems
- Publishing
- E-book sales sites, content posting sites, corporate sites, service sites
- Education
- Research sites, study management sites, corporate sites
- Entertainment & Sports
- Members-only sites, online retail sites, ticket reservation sites
- Communications
- Corporate sites, service sites, communication systems